Fight against fraud
Detect fraud attempts in real time. Protect your customer journeys without complicating the user experience.
They trust us



What is the fight against fraud?
The fight against fraud aims to detect and prevent attempts at identity theft, document falsification and data manipulation.
An automated device makes it possible to identify weak signals and protect your operations while maintaining the customer experience.
Proactive detection
Reinforced protection
Real-time control
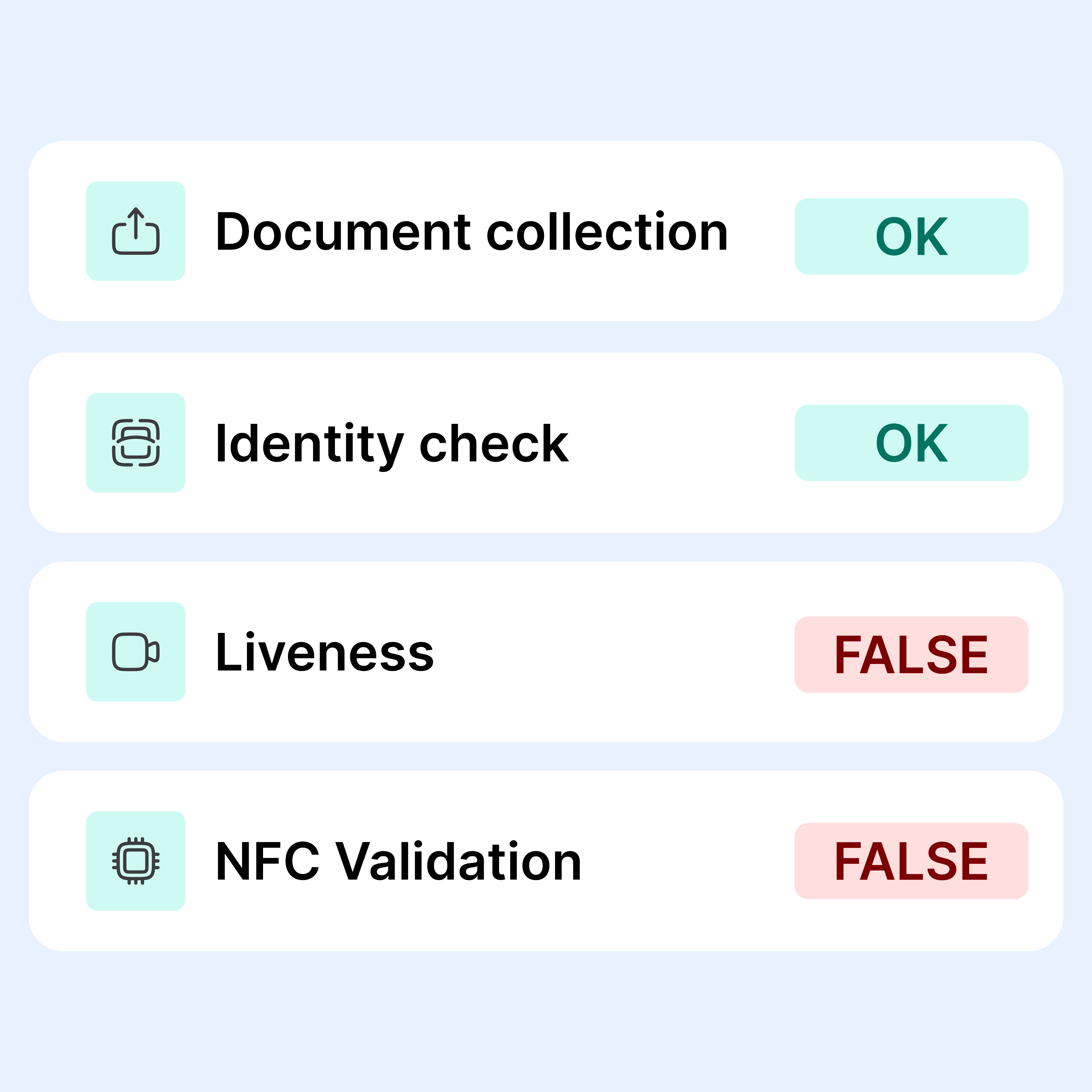
Anti-fraud device
The checks are carried out automatically, from the documentary analysis to the operational decision. You benefit from real-time detection, without slowing down your customer journeys.
Document analysis
Each document transmitted is examined for alterations, inconsistencies or manipulations.
The checks cover both the visible content and the technical structure of the file in order to identify advanced falsifications.
Multi-criteria analysis
Reported information and user metadata are analyzed to identify atypical patterns.
Weak signals are identified through the cross-referencing of information and the application of dynamic risk rules.
Decision and protection
In the event of a proven risk, automatic actions are triggered according to your anti-fraud policy.
Suspicious cases can be blocked, put on hold, or escalated to your specialized teams for investigation.
Identify advanced falsifications
Analyze each document transmitted to detect manipulation attempts. Combine visual, structural, and technical checks to spot sophisticated fraud. Secure the integrity of parts as soon as they are received.
Alterations
Detect changes, edits, or deletions of sensitive items. Identify inconsistencies that are invisible to the naked eye.
Coherence
Automatically compare data between multiple documents. Point out critical contradictions.
Metadata
Analyze the technical information of the files transmitted. Identify generation or editing anomalies.
Integrity
Verify the structure and security features of the document. Increase the reliability of validated supporting documents.
Spot weak fraud signals
Identify unusual behaviors and suspicious data combinations. Analyze declarative inconsistencies before validating the file. Reduce risk from the very first interactions.
Facematch
Compare the user selfie to the photo on the ID document to detect impersonation attempts.
Inconsistencies
Identify discrepancies between reported data and documents provided.
Scoring
Assign a dynamic fraud score and risk level to each case.
Location
Analyze the geographic consistency of connections and statements. Detect access from risky or inconsistent areas.
Control the response to fraudulent attempts
Automatically activate the appropriate measures as soon as a risk is detected. Structure your anti-fraud decisions according to your internal policy. Reduce the financial and operational impact of confirmed or suspected fraud.
Blocking
Suspend high-risk cases immediately. Prevent fraudulent paths from being finalized.
Rock climbing
Intelligent routing to your fraud teams. Focus human expertise on critical cases.
Expertise
Have the file reviewed by an anti-fraud and identity verification expert.
Adaptation
Adjust your rules according to the new patterns detected. Maintain a scalable anti-fraud system.

Detect fraud in all its forms
Fraud takes many forms and comes in a variety of forms. Datakeen helps you identify fraud in all its forms.
Counterfeiting
Counterfeiting is the most common type of document fraud. It consists of the complete reproduction of an official identity document.
Identity theft
Identity theft is particularly dangerous for victims. The fraudster uses an identity document belonging to the victim.
Falsification
Falsification involves the modification of an authentic document in a fraudulent manner. You can falsify the validity date, identity information or even the photograph of the document.
Stolen documents
Blank stolen documents are authentic pieces that were stolen before they were awarded. These can then be completed by the fraudster and pass for authentic documents.
Real-time detection of spoof and falsification attempts. Each weak signal is analyzed to stop fraud before it impacts your operations.

Your remediation campaigns
Target incomplete records and automate their updating at scale. Reduce operational burden and maintain a compliant portfolio.
Our latest articles
Stay up to date with the latest news in artificial intelligence, identity verification, and the fight against fraud



